Top 10 Sources of Computer Virus & How to Avoid Them
Sources of Infection Virus
There are various ways in which computer viruses can attack computer system;
- When you download or open attachment in e-mail message or by instant messaging messages
- Installing unknown program from unreliable and suspicious looking web sites
- Illegal duplication of software from one computer to another e.g. computer games etc.
- When you use infected flask h drive or CD-ROMS or DVD on your system
- Viruses can be transmitted from one computer to another e.g through infected diskettes
- Viruses can infect your computer when you download from the internet
- Virus infection can happen through an infection flash disk, hard disk or optical disk. Computers on internet are more prone to virus infection as different types of virus are constantly released and can be downloaded easily into the system.
- Another source of infection can be bad handling of the computer which can cause critical system malfunction e.g. exposing the computer to heat source, severe power fluctuation etc.
Virus Warning Signs
- Slowing down of the response time
- Presence of tiny dots.
- Wandering across the screen.
- Incomplete saving of file.
- Corruption of the system set-up instruction.
- Appearance of strange characters.
- It can cause organized program into a disorganized program and making them not to execute.
- It destroys the partition task file, even the entire system of hard drive.
- Causes damage to valuables stored on any storage media.
- Causing machine to stop and suddenly restarting itself.
- Sudden disappearance of programs and applications from the system without deletion.
- New windows keep opening up at an alarming rate.
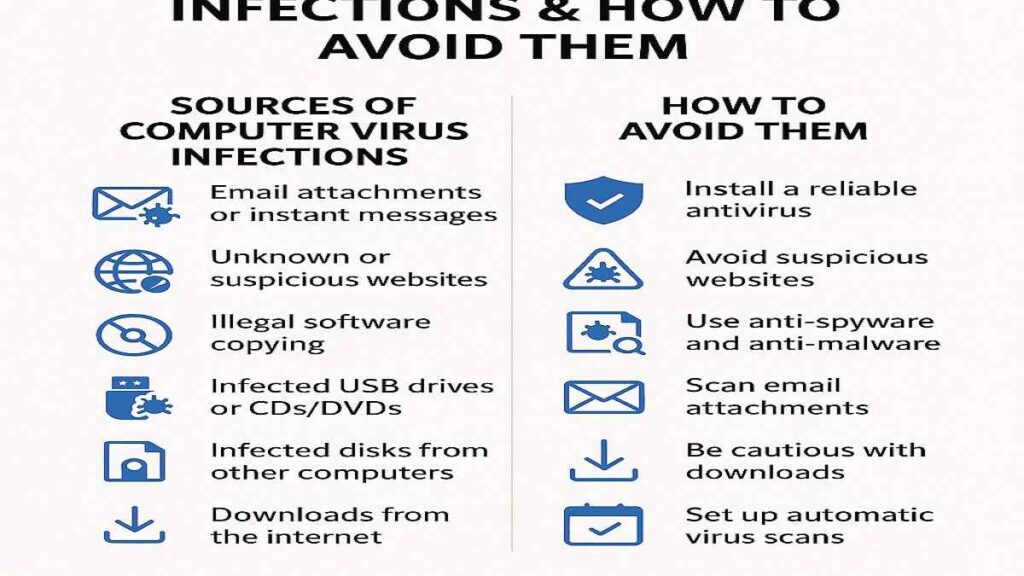
Preventing Computer Virus
- A good and reliable antivirus should be installed.
- Avoid suspicious websites that attempt to install and run a program on your system.
- Install anti-spyware and anti-malware programs.
- Scan any e-mail attachment you want to view and open.
- Watch your download from the internet e.g. music, video and any other items.
- Install firewalls.
- Set-up automatic virus scan.
- Update antivirus regularly.
- Stay away from cracked software and be prepared to lock down anytime you hear of a new virus.
Computer Antivirus
Antivirus is a program developed to destroy computer virus wherever it is found in the system. Examples of antivirus software are:
- Norton antirust
- McAfee virus scan
- Dr Solomon Trolled
- Pennicillin
- Microsoft Antivirus
- Check point Antivirus
- Central point Antivirus
- Avast
- Karpersky
- E-scan
Evaluation:
1. Mention five examples of computer virus.
2. State five sources of virus infect micro computer..
3. State seven virus warning sign.
4. State five ways of preventing computer virus.
READING ASSIGNMENT
Understanding Data Processing for senior secondary schoolsby Dinehin Victoria pages 290 – 292
Questions
- Virus warning sign include the following except ……………(a) Presence of tiny dots.(b) Incomplete saving of file. (c) e-scan (d) Slowing down of the response time
- ………… deletes the information contained in the files.
- Fat virus (b) micro virus (c) Overwrite virus (d) Polymorphic virus
- …………………. prevent access to certain section of the disk where important files are stored and the damage caused can result in information losses from individual files or entire directories (a) Polymorphic virus (b) micro virus (c) overwrite virus (d) Fat virus
- …………..is a program developed to destroy computer virus.
- Anti virus (b) malware (c) spyware (d) virus
- ……………… consumes or occupy a large part of computer memory thereby causing network servers and individual computers to stop responding.
- Trojan horse (b) worm (c) spyware (d) malware
THEORY
- Define computer virus.
- State three ways in which virus can infect micro computer.
- State five sources of virus infect micro computer..
- State five ways of preventing computer virus.
- State five examples of anti virus
References
CISA – Cybersecurity & Infrastructure Security Agency
NIST – Malware Incident Prevention & Handling Guide (PDF)
See also:
Top 10 Computer Viruses You Should Know About
Network: Benefits, Internet Security, Internet Abuse, Intranet & Extranet
Computer Networks: Types, Topologies, and Benefits
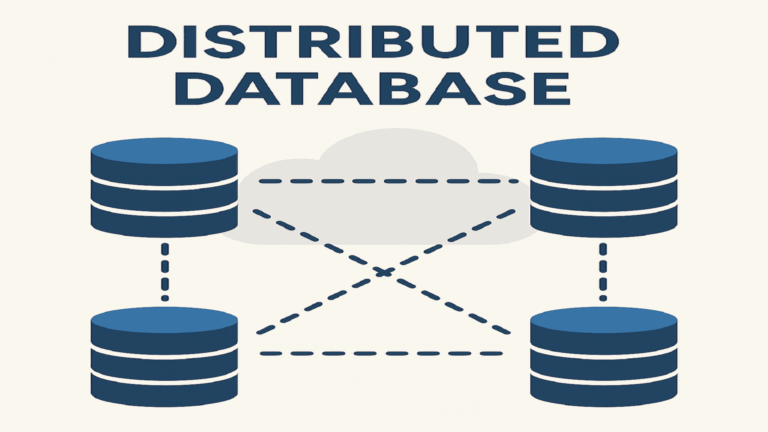
What is a Distributed Database? Definition, Types, and Architecture Explained
Parallel Databases: Architecture, Advantages, and Implementation
Samuel Okeke is a highly experienced and skilled Website Developer, Computer Lecturer, IT Instructor, Digital Marketing Expert, Computer Engineer, and Author with over a decade of experience in the educational, digital marketing and IT sectors. He has proven track records of developing and sustaining successful educational projects, including Acadlly, Audio School, and Certifications Exam Prep. He possess a strong passion for education and a commitment to making a positive impact on people and society.